DORA Compliance 2026: Key Requirements Explained
DORA Compliance: A Strategic Guide for the Financial Sector
Learn how the Digital Operational Resilience Act reshapes EU financial sector ICT risk. Expert guide to DORA compliance, penalties, and strategic advantage.
What Is DORA and Why Does It Matter?
Regulation (EU) 2022/2554, commonly known as DORA, was adopted on December 14, 2022, and became fully applicable on January 17, 2025. This DORA regulation establishes a unified, comprehensive framework designed to eliminate the regulatory fragmentation that previously allowed ICT risks to be managed inconsistently across the European Union's financial services sector. Before DORA, operational resilience requirements were scattered across sector-specific directives, creating key gaps that left the financial system vulnerable to systemic ICT failures and sophisticated cyberattacks.
The regulation addresses this by harmonizing ICT risk management rules across all types of financial entities, ensuring that the entire ecosystem — from global banks to crowdfunding platforms — operates under a single, coherent set of digital resilience standards. As the European Insurance and Occupational Pensions Authority (EIOPA) explains, DORA brings harmonized rules relating to operational resilience applicable to 20 different types of financial entities and ICT third-party service providers.
The Five Pillars of the DORA Framework
The regulation is built upon five core pillars (the five pillars) that define the technical and organizational requirements for covered entities. Understanding each pillar is essential for building a comprehensive compliance strategy and a clear path from gap assessment to sustained operational maturity.
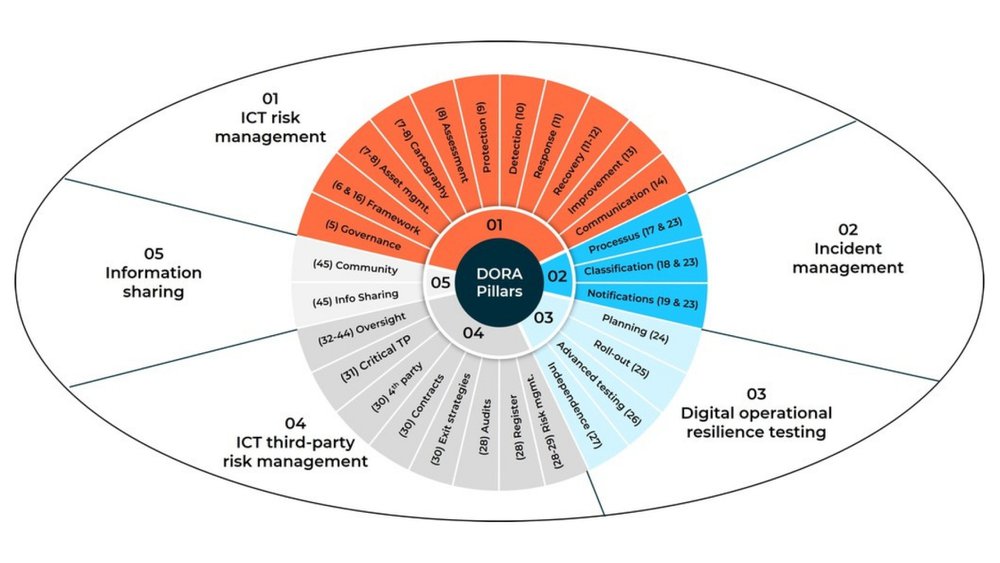
Pillar 1 — ICT Risk Management (Articles 5–16) requires financial institutions to implement a robust framework covering the identification, protection, detection, response, and recovery from ICT risks. The management body bears ultimate accountability for approving and overseeing this framework, including business continuity and disaster recovery plans, and ensuring effective ICT risk management to minimize potential ICT disruptions.
Pillar 2 — Incident Management and Reporting (Articles 17–23) mandates the classification of ICT incidents using standardized criteria and the reporting of major incidents to competent authorities. Entities must follow a structured notification process: an initial notification, an intermediate report, and a final report. In practice, this means building repeatable incident response cases for significant incidents and establishing thresholds for significant ICT-related incidents.
Pillar 3 — Digital Operational Resilience Testing (Articles 24–27) requires regular basic testing such as vulnerability assessments and network security reviews. Significant entities must also conduct advanced threat-led penetration testing (TLPT) on live production systems at least every three years, using external threat intelligence providers. Many programs formalize this as resilience testing, combining regular testing, impact assessments, and “lessons learned” remediation to demonstrate high digital operational resilience under regulatory scrutiny.
Pillar 4 — ICT Third-Party Risk Management (Articles 28–44) obliges firms to maintain a comprehensive Register of Information (RoI) documenting all ICT third-party arrangements. This register must be submitted annually to competent authorities by March 31. Contracts with ICT providers must include mandatory provisions covering exit strategies, audit rights, and security requirements. For many firms, this is the center of operational third-party risk management (including oversight of critical service providers) and an expanding oversight framework for supplier governance.
Pillar 5 — Information Sharing (Articles 45–49) encourages the voluntary exchange of cyber threat intelligence among financial entities to strengthen collective defense mechanisms across the sector, including cybersecurity-related information communications and frontline intelligence on emerging attack patterns.
Who Must Comply: Understanding the Scope
The scope of DORA is exceptionally broad. Article 2 of the regulation applies to 21 distinct categories of entities, encompassing virtually the entire EU financial ecosystem. The following table summarizes the key entity types covered.
| Credit and payment institutions | Banks, payment service providers, e-money institutions |
|---|---|
| Investment and trading entities | Investment firms, trading venues, central counterparties |
| Insurance sector | Insurance and reinsurance undertakings, intermediaries |
| Fund management | Alternative investment fund managers, management companies |
| Market infrastructure | Central securities depositories, trade repositories, credit rating agencies |
| Emerging sectors | Crypto-asset service providers, crowdfunding platforms |
| Technology providers | ICT third-party service providers, including designated CTPPs |
Table 1: The key entity types covered in DORA
While the regulation is expansive, it incorporates a principle of proportionality. Requirements are scaled according to an entity's size, overall risk profile, and the complexity of its operations. Microenterprises and certain smaller entities benefit from a simplified ICT risk management framework under Article 16, ensuring that the regulatory burden remains manageable while still achieving the core objective of digital resilience.
Enforcement, Penalties, and the End of the Grace Period
With the regulation fully applicable since January 17, 2025, the informal tolerance period has concluded. National Competent Authorities (NCAs), alongside the European Supervisory Authorities (ESAs), are now conducting active enforcement reviews. In 2026, regulators have moved from reviewing paperwork to demanding proof — real-time evidence of resilience, automated reporting, and demonstrable control over ICT risk (including complete, defensible data lineage for key reporting fields in the RoI).
The penalties for non-compliance are severe and designed to compel immediate action. The table below outlines the penalty framework.
| Financial entities | Up to 2% of total annual worldwide turnover |
|---|---|
| Critical ICT third-party providers | Fines up to EUR 5 million, plus periodic penalty payments |
| Senior management (individuals) | Personal fines up to EUR 1 million; temporary management bans |
Table 2: The penalty framwork of DORA
Penalty implementation varies significantly among Member States. Italy has set ceilings of up to EUR 20 million or 10% of annual turnover, while Ireland allows fines up to EUR 10 million or 10% of turnover. Germany and the Netherlands differentiate between intentional and negligent breaches, and Article 52 of DORA allows Member States to impose criminal penalties for severe violations, including imprisonment in extreme cases. This divergence, documented in a comprehensive DLA Piper analysis of penalty regimes, makes a proactive and jurisdiction-aware approach to compliance essential.
Latest Developments: What Changed in 2025 and 2026
The regulatory landscape around DORA has evolved rapidly since the regulation became applicable. Several developments are shaping the compliance environment in 2026 and influencing implementation priority tasks for compliance teams.
In November 2025, the ESAs published their first list of 19 designated Critical ICT Third-Party Providers (CTPPs), including Amazon Web Services, Google Cloud, Microsoft, Oracle, SAP, and Deutsche Telekom. These providers are now subject to direct EU oversight, including annual risk assessments, on-site inspections, and mandatory reporting. Financial institutions that depend on these providers must demonstrate they have assessed and mitigated the concentration risk arising from those dependencies as part of the new DORA requirements.
The second annual Register of Information submission cycle concluded in March 2026, with national deadlines varying across jurisdictions. The 2025 pilot round exposed serious friction — many firms discovered they lacked a centralized view of their ICT vendor relationships, with contracts scattered across procurement teams, business units, and subsidiary operations. According to research by Deloitte, 46% of financial entities named the Register of Information as the single most challenging DORA requirement, often due to the most common barriers: inconsistent vendor metadata, incomplete contract inventories, and unclear ownership of additional components like subcontractors and intra-group ICT services.
In January 2026, Germany's BaFin issued non-binding guidance clarifying how AI-based systems must be integrated into DORA-compliant ICT risk management frameworks. This guidance confirms that AI systems — particularly generative AI and large language models — are not subject to a separate regime but must be fully embedded into existing ICT governance, testing, and third-party risk frameworks (including documentation of key focus areas such as model monitoring, access controls, and resilience testing for AI applications). Nordic NCAs have similarly prioritized digital resilience as a top supervisory focus for 2026.
DORA and the Broader EU Regulatory Landscape
DORA does not operate in isolation. It forms part of an interconnected web of EU digital regulations, and understanding these relationships is critical for efficient compliance. DORA functions as lex specialis for the financial sector, meaning it takes precedence over the NIS2 directive for in-scope entities. Where NIS2 sets baseline cybersecurity requirements across critical sectors, DORA imposes more specific and stringent obligations tailored to financial services.
The regulation also intersects with the EU AI Act. Article 9(10) of the AI Act explicitly permits the integration of AI risk management systems into DORA ICT risk management procedures, enabling financial entities to build a unified governance framework rather than maintaining parallel compliance structures. This creates a significant opportunity for organizations that approach compliance strategically, reducing audit fatigue and streamlining governance across multiple regulatory frameworks and state- level mechanisms (such as national supervisory expectations and local enforcement practices). For organizations navigating these overlapping requirements, understanding the EU AI Act alongside DORA is essential.
Transforming Regulatory Requirements into Strategic Advantage
Viewing DORA merely as a compliance exercise is a missed opportunity. Forward-thinking organizations are leveraging these requirements to drive operational excellence and build digital trust with their clients, partners, and regulators. The compliance costs are significant — research indicates most institutions spend between EUR 2 million and EUR 5 million, with 70% expecting permanently higher run costs for technology controls — but the cost of non-compliance is far greater.
Organizations that treat the regulation as a catalyst for operational improvement gain several strategic advantages. A robust ICT risk management framework does not merely satisfy regulators; it genuinely strengthens an organization's ability to detect, respond to, and recover from cyber incidents. Comprehensive third-party risk management reduces vendor concentration risk and improves supply chain resilience. Structured incident reporting accelerates response times and minimizes the operational and reputational impact of ICT disruptions.
Crucially, DORA readiness often starts with a pragmatic gap assessment to identify key gaps, map specific requirements to existing controls, and align evidence collection to the RTS standards and supervisory expectations. This approach reduces rework, supports faster implementation, and helps teams prioritize remediation that materially improves cybersecurity outcomes across systems, data, applications, and networks.
By prioritizing AI regulatory compliance and integrating it with these requirements, financial institutions can transform mandatory risk management into a competitive differentiator — demonstrating to clients and counterparties that their operations are secure, resilient, and governed to the highest standards.
Navigate DORA with Confidence
Achieving full compliance with DORA requires deep regulatory expertise and a strategic approach to digital operational resilience. The transition from paperwork to verifiable proof is challenging, but you do not have to navigate it alone.
Nemko Digital provides the authoritative guidance and practical solutions necessary to ensure your systems are secure, resilient, and fully compliant. Whether you need to align your ICT risk management framework with DORA's five pillars, integrate AI governance into your compliance structure, or prepare for supervisory examinations, our team delivers clarity and actionable results. Explore our AI governance standards and compliance insights to take the next step toward turning regulatory obligations into long-term strategic value.
Future-Ready Solutions
Nemko Digital’s AI governance and regulatory compliance experts help organizations navigate current and upcoming regulatory frameworks, ensuring readiness for the future.
Contact Us.webp)
.webp)